Anonymous
email, often referred to as prank email (or fake email), allows the
user to send an email without disclosing their identity. The system
uses a simple input form on a web page. Information is entered filling
out the elements of a real email. Sender's and recipient's email
addresses, subject and message body are usually the minimum required
fields. Clicking on the send or submit button activates a script
formats the information and then sends out the bogus text with the
system mail utility. The recipient opens a real looking email from the
fake address and reads the prank content. Prank email's primary purpose
invol
...
Read more » Anonymous
email, often referred to as prank email (or fake email), allows the
user to send an email without disclosing their identity. The system
uses a simple input form on a web page. Information is entered filling
out the elements of a real email. Sender's and recipient's email
addresses, subject and message body are usually the minimum required
fields. Clicking on the send or submit button activates a script
formats the information and then sends out the bogus text with the
system mail utility. The recipient opens a real looking email from the
fake address and reads the prank content. Prank email's primary purpose
invol
...
Read more »
|
|
Su ... Read more » |
|
|
 |
|
Iguess students from LovelY Professional University and from other universities are helpless in terms for opening orkut and facebook. So here is the tute to bypass any firewall without any third party software
Here is a complete Graphical tutorial for using Free Proxy with Firefox. By using a Proxy, you can browse internet anonymously. Also a proxy can be used for browsing blocked sites like Orkut and MySpace. Step 1. Find a list of free proxy. You can Google it out. One such list is here. Step 2. Now choose an IP address and port from this list. In this tutorial I have chosen IP: 195.175.37.6 and port: 8080. You can choose whatever you like. 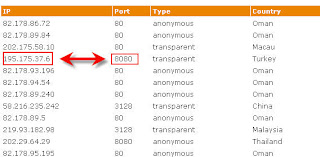 ...
Read more »
...
Read more »
|
 Black Berry,one of the leading enterprise phone available
on earth. But with its groundbreaking advantages it also have many disadvantages
( ya you heared right, i said MANY ), but yup here are some of them...
Lovely professional university,Rahul Tyagi, LPU Black Berry,one of the leading enterprise phone available
on earth. But with its groundbreaking advantages it also have many disadvantages
( ya you heared right, i said MANY ), but yup here are some of them...
Lovely professional university,Rahul Tyagi, LPU
1. No
Wi-Fi – With the iPhone 3G, you can surf at home, countless free
hotspots (McDonalds anyone?), or take advantage of an O2 tariff with
all-you-can-eat Wi-Fi. Sadly there’s n
...
Read more »
|
 Feel Free To Contact Us For Ethical Hacking Queries and For Seminars and Workshops in your college,school,university.
...
Read more »
|
 Hello Friends, most people mailing me to give an article on a new advance bootable operating systemSo here is your new powerfull OS named Hiren's BootCD ,(HBCD) is a completely free bootable CD that contains a load of useful tools you can make use of in a variety of situations like analyzing, recovering and fixing your computer even if the primary operating system can not be booted.
It is a great resource for anyone with computer problems who is having trouble accessing the internet to download programs in an attempt to fix it. It has a multitude of tools divided into ... Read more » |
|
SQL Injection still used by script kiddies , gery and even by black hat hackers, its the easiest way to hack into some one's website. So today in this article i will give you some tips to, how to prevent SQL injection on your own or may be company's website.
1. Don't allow special characters As we all know the SQL strings are often having special symbol strings, making a combination on OR and =. So try to have stroke procedures instead of SELECT * FROM table name where Username="..." and Password="...", This is the global code and vulnerable. So try to validate your code and try to avoid acceptance of special symbols. 2. Use Email Instead of User ID The best way to prevent SQL injection is to have use of Suer name as Email address. So what is happening here the code written will validate in such a way that it will not accept anything else instead of EMAIL address. Thus SQL injection strings are non acceptable hence SQL injection c ... Read more » |
 FREE RECHARGE TRICK  My be you are impressed by the heading "free recharge", usually very popular in orkut forums these days and other social networking websites. But friends this is a trap, what is going on here is that http://sn.imis a yrl shrinker website helps you to make your url shorter, so the link ... Read more » |