...
Read more »
...
Read more »
|
|
Acunetix Web Vulnerability Scanner
 Audit your website security with Acunetix Web Vulnerability Scanner
As many as 70% of web sites have vulnerabilities that could lead to the theft of sensitive corporate data such as credit card information and customer lists Hackers are concentrating their efforts on web-based applications - shopping carts, forms, login pages, dynamic content, etc. Accessible 24/7 from anywhere in the world, insecure web applications provide easy access to backend corporate databases. Firewalls, SSL and locked-down servers are futile against web application hacking! Web application attacks, launched on port 80/443, go straight through the firewall, past operating system and network level security, and right in to the heart of your application and corporat ... Read more » |
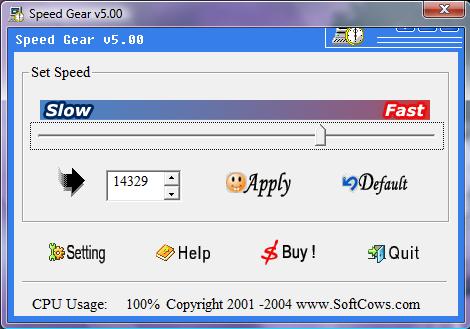 Speed Gear is a fantastic tool to speed up games. It can speed up almost all the games. Speed Gear is easy-to-use, you can press an easily accessible hotkey to speed up game, slow down game or adjust game to the speed you feel most comfortable with. Speed Gear will give you brand new experience while playing games. For example; with this program you can slow down the action games so that you can see the bullet's flight line and avoid it easily. System Requirements ... Read more » |
|
China’s leading search engine claims a shocking lack of security nous at its chosen domain name registrar was responsible for a prolonged outage last month. ... Read more » |
|
If you’ve ever wondered about the flow of your mouse around your computer screen, a free downloadable application, called "mouse pointer track,” can help you follow these esoteric movements and turn them into a fascinating blur between art and information. ... Read more » |
 Monster botnet held 800,000 people's details
|
 We are looking for persons who are willing to publish their articles based on ethicalhacking,network security,computer security and every aspect related to computer. So please send us your articles with your pic and after reviewing we will publish your article on India's Most
emerging ethical hacking website community www.ethicalhacking.do.am
...
Read more »
|
|
The best way to avoid leaving traces of your computer activites on the hard disk is by using RAM memory, you can accomplish this surfing from a live CD, and if you add an anonymous proxy to that live operating sys ... Read more » |
FacemashWell May be you are using facebook from the last 1 2 or 5 years but the question here arises who devolp facebbok. So here is the full article on the history of World's largest social networking site FACEBOOK. |
|
Top Working Proxy Websites
 12.161.122.92:8080 24.22.10.60:10777 38.101.222.129:8080 58.59.2.130:8080 58.59.2.150:8080 60.32.214.122:80 60.217.228.199:80 61.4.110.18:8080 61.11.54.211:6588 61.19.148.233:8080 61.143.61.78:15331 61.241.6.84:8080 62.150.26.53:80 62.150.76.251:80 62.220.12.98:8000 64.76.68.2:3128 64.246.18.25:8888 65.79.56.15:80 65.103.141.124:80 65.206.41.240:80 65.216.115.212:80 66.240.123.59:3128 67.15.199.29:3128 69.62.141.29:3128 69.119.249.186:17235 80.68.100.21:80 80.68.100.22:80 80.68.100.101:80 80.146.238.37:80 80.227.0.153:3128 80.227.47.246:8080 81.181.45.25:3128 81.190.43.90:17235 82.77.191.227:80 82.115.63.190:3128 82.137.247.131:3128 82.137.247.134:80 82.177.125 ... Read more » |