|
|
 Introduction Ostinato is an open-source, cross-platform network packet crafter/traffic generator and analyzer with a friendly GUI. Craft and send packets of several streams with different protocols at different rates. Features Runs on Windows, Linux, BSD and Mac OS X (Will probably run on other platforms also with little or no modification but this hasn't been tested) Open, edit, replay and save PCAP files Support for the most common standard protocols Ethernet/802.3/LLC SNAP VLAN (with QinQ) ARP, IPv4, IPv6, IP-in-IP a.k.a IP Tunnelling (6over4, 4over6, 4over4, 6over6) TCP, UDP, ICMPv4, ICMPv6, IGMP, MLD Any text based protocol (HTTP, SIP, RTSP, NNTP etc.) More pro ... Read more » |
|
Yeah, now you can also search anything,
anytime, anywhere on Google without a internet connection. Google on
your mobile either it’s a Smartphone or low cost phone it will help you
with his SMS service. You don’t need to buy a expensive phone’s out of
your budget to just surf for internet on the go.
Please follow the following step:- 1. You have to just type your keywords (You want to search) in your phone message box (create message). 2.Then add receipt send it to 9773300000. And it will comeback you the answer within a few seconds. 3. You will feel like you are surfing Google on the Internet. It helps me when I went to Delhi with friends at late night and we have to search for movie Showtime’s. Then I messaged on that number movie Delhi. And I stunned, got minimum 12-13 messages about movies Showt ... Read more » |
|
Its my 7th year in this field and trained more than 10k students from all around the world. And what i found is that up to 90% students join the certification course just to know how to hack email id especially FACEBOOK. and there are many more, for those who want know how to hack Facebook ID and other email account hacking, i suggest have a Google search and read and please do not waste your parents money on such stupid things.
A Ethical hacking certification is not for those who want to hack and destroy , Ethical Hackers Profession is a very reputed profession and due to some people , ethical hacker's name is just ruined. Please be responsible to the cyber society around you and devote your time on securing rather than destroying. Ok here is a list of some questions students asked me especially before joining the certification course. 1. Will you teach us how to hack Facebook ID , Gmail , Yahoo ? 2. Will you tea ... Read more » |
|
Its not first time PTU (Punjab Technical University), One of the most famous University in India come down to its knees , when it comes to declaring results to students. and Today as the result declared wit in few hours website goes under Denial of Services Attack (Unintentional) . For those who do not know what is DDOS attack, a DDoS is Distributed Denial of Service attack. To explain it in simple
words, you send many requests to a server and they are of very high
priority requests, then the server would be taking only the requests
sent by you and not by others. In this way, only you (hacker / DDoS guy)
will be served and others will just see 500 Internal Server Error (Too
many connections)! or Page can not displayed kinda of error.
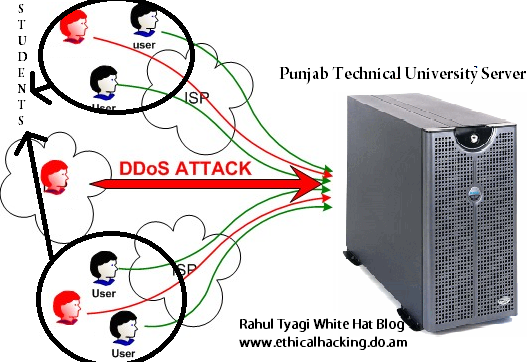 This attack is one of the most dangerous attack and till date having no cheap in cost countermeasure, bottom-line for many organiza ... Read more » |
 SMS Spoofing is today's biggest challenge for every telecom company. In India especially there is not a single company that provides complete protection against SMS Spoofing attack, and this is the thing to worry. Two main reasons are there why all companies are unable to prepare a bulletproof plan against this attack. SMS Spoofing is today's biggest challenge for every telecom company. In India especially there is not a single company that provides complete protection against SMS Spoofing attack, and this is the thing to worry. Two main reasons are there why all companies are unable to prepare a bulletproof plan against this attack.1. Hard Cyber Laws 2. Big Investment on the name of Security Hard Cyber Laws Here we are not talking about the laws for SMS spoofers , but laws for the telecom comapnies to implement a hard tracking gateway for sms spoofing. Untill Govt. issues a hard law to implement the security mechanism telecom companies will not t ... Read more » |
|
...
Read more »
|
 Its a very old trick but i tried to remind it again. In simple login processes the password is written on the password box and
the text became a symbol of the star and sometimes bulatan2 shaped
symbol. For example: (*******). So how we can see the password behind the asterisk symbols. Its a very old trick but i tried to remind it again. In simple login processes the password is written on the password box and
the text became a symbol of the star and sometimes bulatan2 shaped
symbol. For example: (*******). So how we can see the password behind the asterisk symbols.Follow the steps below:-
|
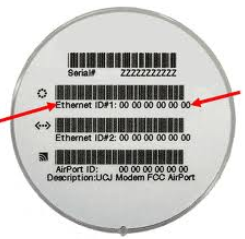 Most people among us change their IP address and thinks they are anonymous on internet but one thing they forgot that they can be tracked down with MAC address which is still there non spoofed. So what to do then? Its practically impossible to change your MAC address but yes virtually its possible :). Here is a application called SMAC that can help you to spoof your MAC address to maintain your anonymity on internet. Most people among us change their IP address and thinks they are anonymous on internet but one thing they forgot that they can be tracked down with MAC address which is still there non spoofed. So what to do then? Its practically impossible to change your MAC address but yes virtually its possible :). Here is a application called SMAC that can help you to spoof your MAC address to maintain your anonymity on internet.SMAC is a powerful, yet an easy-to-use and intuitive Windows MAC Address Modifying Utility (MAC Address spoofing) which allows users to change MAC address for almost any Network Interface Cards (NIC) on the Windows VISTA, XP, 2003, and 2000 systems, regardless of whether the manufacturers allow this option or not. SMAC does not change the hardware burned-in MAC addresses. SMAC changes the "software based" MAC addresses, and the new MAC add ... Read more » |